Gone are those days when organizations had to either invest money in traditional extensive programming for application development or settle for off-the-shelf software. With the tremendous increase in the number of app users, application development has become a high-priority task. Owing to this, low-code platforms are revolutionizing application development and helping organizations speed up the deployment of new applications. Moreover, to meet business needs, companies want enterprise-grade applications that can ensure high performance.
Enabling non-technical users to build applications by adopting drag-and-drop components without any help from IT, definitely provides ease of usage. But are low-code platforms entirely secure? Is it not risky to entrust more power to citizen developers who have less security training? Are there any hidden vulnerabilities that are compromising your business security? This is a crucial aspect to watch out for any organization when selecting a low-code platform.
Low-code platforms offer standardized functions for specific sectors such as security, integration, and data protection. The development processes are transparent which makes it a low-risk project and any inconsistencies are resolved immediately at earlier stages. However, low-code platforms can be a big risk to your security if they are being deployed on a private hosting site. Low-code platforms can be less secure when developers build few parts of their app outside the inherent environment of the low-code platform.
In comparison to the traditional applications, low-code platforms are more secure since the full-cycle development is hosted on the vendor’s secure cloud platform. Restricting the kind of data that can be shared is one step towards securing sensitive information, but sometimes end-users are in a position to make such decisions, which makes the task of guarding sensitive data a bit more challenging.
4 ways to strengthen low-code environment security
-Oct-07-2021-10-32-25-71-AM.png?width=823&name=MicrosoftTeams-image%20(6)-Oct-07-2021-10-32-25-71-AM.png)
Secure Design: A voluntary effort and acknowledgment are needed towards implementing security features. Sensitive data such as Social Security Number must be encrypted before storing in the database to ensure there is no accidental exposure of such sensitive data.
Threat Modelling: Reviewing all the entry points of the system, threats, and assets to determine whether the design successfully mitigates all the potential risks.
Static code Analysis: Reviewing the code to make sure that it follows the accepted industry standard structure. Performing a static analysis to test for common errors and checking whether it interacts with outside sources or not.
Security Testing: Instead of verifying the function that it is intended to perform; security testing involves checking for the functions that the software isn’t designed to do. To perform such testing, the tester tries to understand the common vulnerable points that the attackers might use.
Growing demand for Low-code in application development
When it comes to low-code, it is commonly observed that since low code is used for prototyping so it is considered low-risk. As low-code is permeating in more and more applications, it is crucial to mitigate any flaws in the system to lower the potential risk.
According to Gartner, “By 2024, low-code application development will be responsible for more than 65% of application development activity”.
Application development is high in demand and to sustain speed, performance and massive scaling are the key drivers. But are the low code platforms on which this app is developed scalable? Can these platforms support multiple developers and manage the varying workload? Are you able to extract the true value from the low-code that you are using to its maximum threshold?
To ensure that you are following the best practices in terms of performance and design abiding by the industry standards, make sure that the low-code platform has a well-defined API that separates the backend layers and UI to allow application development at scale. Customarily, to modernize the monolithic legacy apps, generally, the low-code platforms should have faster API creation and documentation.
A flexible low-code platform is the one that uses cloud-based architecture as it can be scaled in terms of design. A cloud-based architecture allows users to build flexible systems, and support continuous delivery. While selecting a low-code platform, certain must-have features should be considered to make well-informed choices. One of such pivotal issues is vendor lock-in when the company becomes dependent on the low-code platform so much to an extent where it is impossible to switch to another platform without incurring tremendous switching costs. To avoid this, it is advisable to document all the activities performed on the platform regularly and keeping separate data and workflow layers.
According to an application development report, 13% of potential users of the low-code platform are hesitant because of their concerns regarding the scalability of the platform. Low-code platforms are equipped with appealing features like visual modeling, a drag-and-drop interface, and out-of-the-box functions like providing sales process management and service management. But these features aren’t sufficient if the platforms aren’t secure enough to protect the applications that the end-users are creating. Moreover, the platform should be scalable enough to accommodate a sudden rise in users due to expansion.
How a low-code platform can deliver enterprise scalability?
Low-code platforms can deliver both run-time and dev-time scalability. Dev-time scalability enables multiple developers to program different use cases across teams and geographies to deliver long-term and interconnected portfolios of applications. This ability of a low-code platform to align with the developmental need of the organizations is dev-time scalability. There are certain features associated with dev-time scalabilities, such as,
- Easy onboarding of new developers to the platform
- Allows role-based access
- Simpler collaboration for citizen developers and programmers
- Ability to add custom code to the developed application
- Wide-range of collaboration tools for easier replication of pre-built elements
- Easier communication and integration with pre-existing tools
Run-time scalability allows a large volume of users to perform compute-intensive operations at the highest standards of reliability and efficiency. This ability of the applications built on low-code platforms to provide fast-user experiences is run-time scalability. Certain features associated with run-time scalability are:
- Faster deployment with automated tasks
- Enables rapid development with containerization
- Easier deployment to any cloud, multi-cloud, or hybrid-cloud environments
- Integration with CI/CD pipelines
- Allowing the developer to deploy applications on-demand independently
Apart from the above-mentioned features for dev-time and run-time scalability that the low-code platform can offer, its role in application scalability is limited. In order to use a low-code platform at full potential, make sure that architectural needs and internal processes are aligned towards scalability. Adjust platform capacity while setting up to meet demands and identify the app deployments permitted beforehand, as per the license terms. Make agile teams and select microservices architectural models instead of using different architectural designs to reduce the time spent in managing, validating, and fixing large application systems. The whole idea of scalability, in a way, revolves around the ability to develop applications faster. Since conventional manual coding is costly, time-consuming, and difficult, faster application development in less time, incidentally lowers the cost of the process.
Innominds Low-Code, No-Code Solution
If security and scalability are important concerns for your enterprise application, create architectural designs and internal processes and align them with a low-code platform. Innominds’ low-code no-code platform, iSymphonyTM, unlike other platforms, doesn’t lock you with proprietary code, infrastructure, and tech stacks. Users can avoid vendor lock-in with iSymphonyTM and create secure enterprise-grade applications smoothly. Leveraging iSymphony TM accelerators, a large battery manufacturer was able to save 320 person-hours of development time while building a service support application.
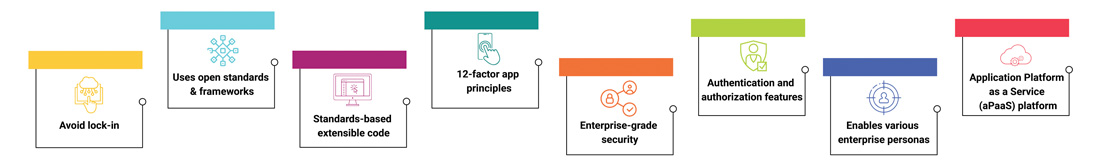
Key Benefits
- Avoids any type of lock-in
- Uses open standards & frameworks, platform & language agnostic code generators, and cloud-agnostic accelerators
- Standards-based extensible code
- Follows 12-factor app principles that create high-quality, clutter-free code similar to human-generated code
- Enterprise-grade security
- Secures apps with authentication and authorization features such as role-based and permission-based access control
- Application Platform as a Service (aPaaS) platform
- Enables various enterprise personas throughout the application lifecycle, from ideation and development through deployment and operation
Accelerate application delivery by 35-40% with web and mobile app development on iSymphonyTM low-code platform. Let’s take you through a free demo!